This article explores the causes for informality in war termination and advocates for a return to formality. Forever wars are a new, pervasive problem. Around the world, conflicts have been simmering and occasionally boil over. They do not seem to end, and this is not normal. International law scholars debate why this is happening, pointing… Continue reading From Treaties to Tweets: The (In)Formality of War Termination
Tag: International Law
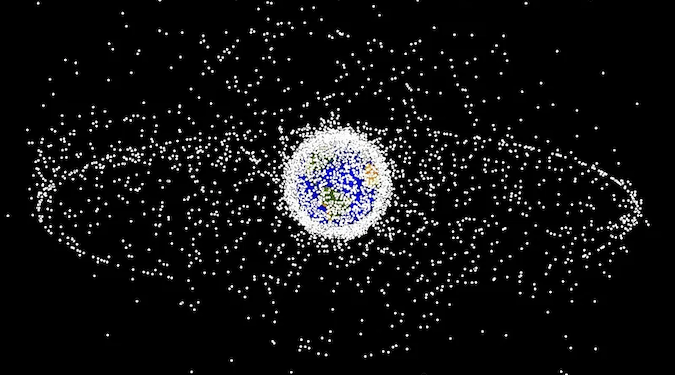
The Role of Regulatory Frameworks in Balancing Between National Security and Competition in LEO Satellite Market
Matin Pedram and Eugenia Georgiades compare existing regulatory frameworks for Low Earth Orbit (LEO) satellites and argue none are robust, transparent, or efficient enough yet to curb monopolistic or rent-seeking behaviors. Likewise, Pedram and Georgiades reveal how national security concerns can be overextended to instead protect domestic space activities. Pedram and Georgiades analyze licensing requirements,… Continue reading The Role of Regulatory Frameworks in Balancing Between National Security and Competition in LEO Satellite Market
Will Soper Responds to Tyler Smotherman’s Review of “Greytown Is No More!”
I have read Tyler Smotherman’s review of my book, Greytown Is No More! I am much buoyed by the many positive passages to be found throughout its 17 pages. I wish to thank the reviewer, Tyler Smotherman, JNSLP Managing Editor Todd Huntley, and Editor-in-Chief William C. Banks for their efforts. I would like to take… Continue reading Will Soper Responds to Tyler Smotherman’s Review of “Greytown Is No More!”