I have read Tyler Smotherman’s review of my book, Greytown Is No More! I am much buoyed by the many positive passages to be found throughout its 17 pages. I wish to thank the reviewer, Tyler Smotherman, JNSLP Managing Editor Todd Huntley, and Editor-in-Chief William C. Banks for their efforts. I would like to take… Continue reading Will Soper Responds to Tyler Smotherman’s Review of “Greytown Is No More!”
Category: International Security
Commissions Impossible: How Can Future Military Commissions Avoid the Failures of Guantanamo?
Aaron Shepard endeavors to examine the roots of the failures of the Guantanamo military commissions and suggest potential solutions to remedy them. His paper begins with an introduction to the concept of military commissions, including a brief overview of their historic utilization and import. It then provides a detailed background on Guantanamo Bay, covers the… Continue reading Commissions Impossible: How Can Future Military Commissions Avoid the Failures of Guantanamo?
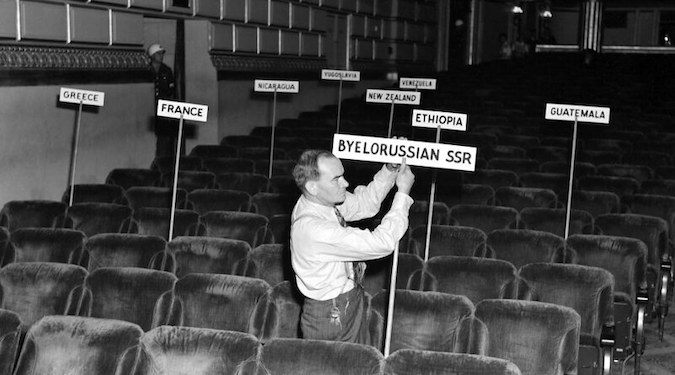
The San Francisco Conference and the Evitable UN Vetoes
Robert A. James reviews the surprising history of the United Nations Security Council veto, the five permanent members solution, and the various alternatives proposed during the discussion. Although the current Security Council format appears historically inevitable, there is ample evidence of alternative formats suggested at the time of the construction of the United Nations. Beginning… Continue reading The San Francisco Conference and the Evitable UN Vetoes