In this book review of Paul Lushenko and Shyam Raman’s The Legitimacy of Drone Warfare: Evaluating Public Perceptions, Joseph Chapa examines how the authors purport to do four things: 1) deliver empirically verifiable differences in how citizens of various countries perceive the legitimacy of drone warfare (in this case, the US and France); 2) offer… Continue reading The Legitimacy of Drone Warfare: Evaluating Public Perceptions
Category: Remote Targeting/Targeted Killing
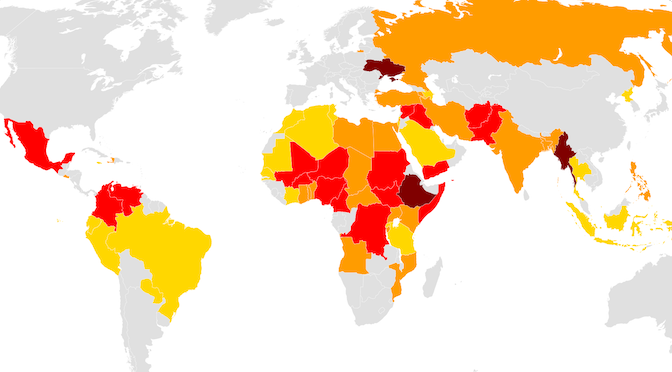
Managing the Terrorism Threat with Drones
The contours of America’s counterterrorism strategy against al Qaeda and the Islamic State have remained remarkably consistent over the past two decades, broadly focused on degrading al Qaeda’s and the Islamic State’s external attack capabilities and global networks, disrupting their operations through military operations or enhanced law enforcement and border security, and denying them sanctuaries.… Continue reading Managing the Terrorism Threat with Drones
Endless War Challenges Analysis of Drone Strike Effectiveness
Whether counterterrorism drone strikes are effective is one of the major questions currently facing US policymakers. The objectives offered as justifications for these strikes are arguably vague and over-broad and therefore run the risk of taking on an endless character. David Sterman argues that “endlessness” is a hazard that has not been appropriately addressed by… Continue reading Endless War Challenges Analysis of Drone Strike Effectiveness