Rebecca Myshrall examines how President Donald J. Trump’s first administration marked a significant shift in the US stance toward the North Atlantic Treaty Organization (NATO), with unprecedented criticism focused on the financial contributions of European allies. Myshrall summarizes the historical context of NATO’s formation and evolution of the US perspectives on it. Myshrall then documents… Continue reading Trump and NATO: Will NATO Survive Under a Second Trump Administration?
Tag: National Security
Hard Cash and Easy Money: Funding Authority for Security Force Assistance Brigades
Maj. Kier Elmonairy evaluates how well today’s security force assistance (SFA) fiscal authorities support the Army’s Security Force Assistance Brigades (SFABs) in conducting their critical mission in an era of great power competition. Elmonairy first surveys the organizations the Army uses to conduct SFA, looking at how Army Special Forces and SFABs complement each other… Continue reading Hard Cash and Easy Money: Funding Authority for Security Force Assistance Brigades
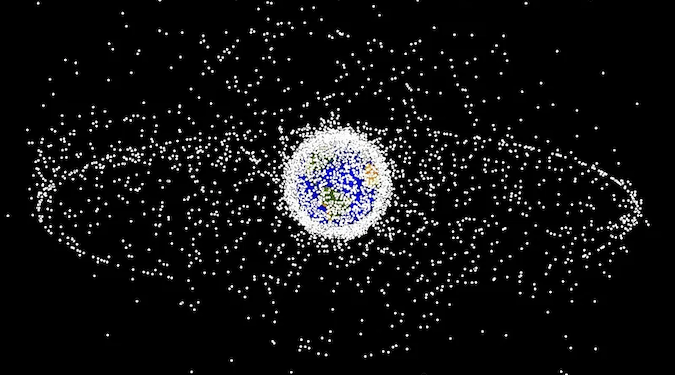
The Role of Regulatory Frameworks in Balancing Between National Security and Competition in LEO Satellite Market
Matin Pedram and Eugenia Georgiades compare existing regulatory frameworks for Low Earth Orbit (LEO) satellites and argue none are robust, transparent, or efficient enough yet to curb monopolistic or rent-seeking behaviors. Likewise, Pedram and Georgiades reveal how national security concerns can be overextended to instead protect domestic space activities. Pedram and Georgiades analyze licensing requirements,… Continue reading The Role of Regulatory Frameworks in Balancing Between National Security and Competition in LEO Satellite Market