Christopher Mohr analyzes the opportunities and hacking and other risks of incorporating machine learning into military logistics and identifies legal and security gaps that make incorporation difficult. Mohr begins by providing background on artificial intelligence and machine learning and describes how these tools can improve military logistics. Mohr also identifies types of cyberattacks that states… Continue reading Zero-Day Delivery: Hacking Risks and the Use of Machine Learning for Military Logistics
Category: Emerging Technology
National Security and Competition: How Courts Evaluate National Security When Assessing a Merger
Michael McLaughlin examines the effect of defense mergers on the national security sphere, arguing that antitrust and national security are largely complementary in accomplishing the goals relevant to each. In “National Security and Competition,” McLaughlin first discusses concerns that come with stifled competition in the defense market. He then focuses on the evolution in case… Continue reading National Security and Competition: How Courts Evaluate National Security When Assessing a Merger
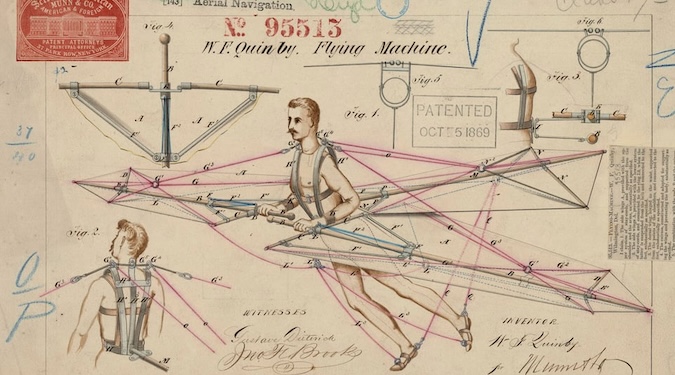
Should the DoD Go Marching-in? US Innovation Leadership & DoD IP Rights
Ebony Christian examines the potential role of the Bayh-Dole Act in national security-related technological innovation and IP rights with a focus on the Department of Defense’s (DoD) interest in leveraging private-sector technology. Christian prefaces her discussion with an emphasis on the need for the United States to stay ahead of its adversaries to preserve its… Continue reading Should the DoD Go Marching-in? US Innovation Leadership & DoD IP Rights