In this book review of Paul Lushenko and Shyam Raman’s The Legitimacy of Drone Warfare: Evaluating Public Perceptions, Joseph Chapa examines how the authors purport to do four things: 1) deliver empirically verifiable differences in how citizens of various countries perceive the legitimacy of drone warfare (in this case, the US and France); 2) offer… Continue reading The Legitimacy of Drone Warfare: Evaluating Public Perceptions
Category: Book Reviews
Will Soper Responds to Tyler Smotherman’s Review of “Greytown Is No More!”
I have read Tyler Smotherman’s review of my book, Greytown Is No More! I am much buoyed by the many positive passages to be found throughout its 17 pages. I wish to thank the reviewer, Tyler Smotherman, JNSLP Managing Editor Todd Huntley, and Editor-in-Chief William C. Banks for their efforts. I would like to take… Continue reading Will Soper Responds to Tyler Smotherman’s Review of “Greytown Is No More!”
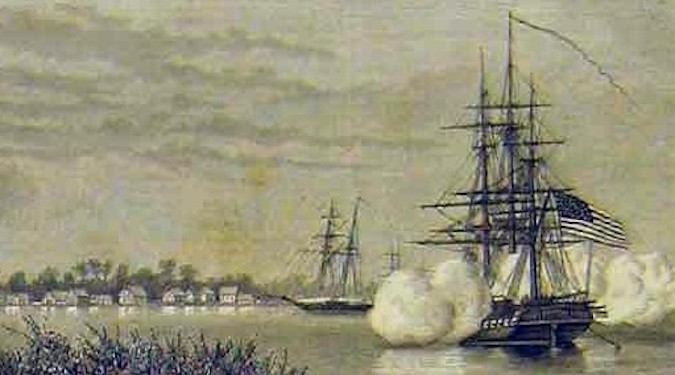
Greytown, Great Power Politics, and History’s Grey Areas
Tyler R. Smotherman reviews Will Soper’s “Greytown Is No More!” The 1854 Razing of a Central American port, the U.S. Businesses Behind Its Demise, and the Lasting Foreign Policy Legacy, which looks at the cause of Greytown’s destruction and takes a critical look at the court’s subsequent ruling in Durand v. Hollins. Smotherman praises the… Continue reading Greytown, Great Power Politics, and History’s Grey Areas