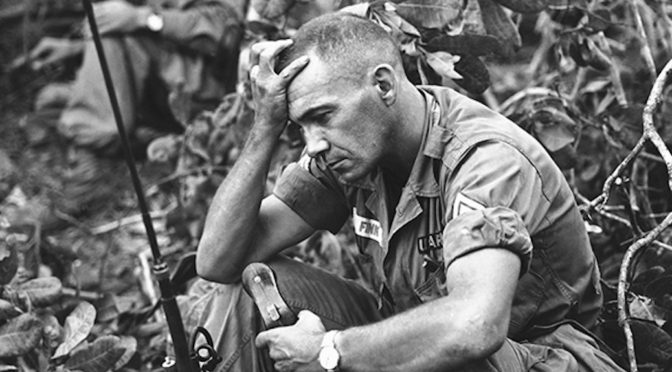
The business that we are all somehow associated with—of contemplating war, preparing for war, deterring war, initiating war, prosecuting war, providing relief in war, ending war, recovering from war—is consequential. Getting as right as possible the intricate dance of decisions that define the initiation, conduct, and conclusion of warfare is incredibly important for societies. It… Continue reading Just War and Conduct in War: An Airman’s Reflection
Category: Vol. 9 No. 2
Before Privacy, Power: The Structural Constitution & the Challenge of Mass Surveillance
The rich legal literature that has grown up to assess the constitutionality of bulk communications collection by the government has focused overwhelmingly—and understandably—on the challenge such programs pose to particular claims of individual right against the state, yet attempting to describe what seems troubling about bulk collection in terms of individual rights alone has significant… Continue reading Before Privacy, Power: The Structural Constitution & the Challenge of Mass Surveillance
Understanding Cyber Collateral Damage
In this article, Sasha Romanosky and Zachary Goldman address the problem of how to define “collateral damage” in the cyber realm. Arguing that unintended effects on data alone can constitute collateral damage, Romanosky and Goldman propose ways for the US military and law enforcement to conceptualize and estimate collateral damage in the context of cyber operations. Understanding… Continue reading Understanding Cyber Collateral Damage