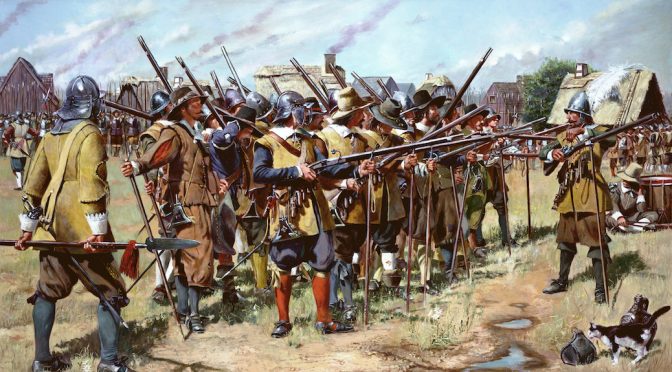
Today, writes Ben Daus-Haberle, the Militia Clauses of the Constitution lead a curious double life. The Second Amendment’s preamble stars in gun rights debates, but when the conversation shifts to the War Powers, these Clauses drop almost entirely from view. The result is a War Powers literature strikingly silent about the Militia Clauses. Yet the… Continue reading The Militia Clauses and the Original War Powers
Tag: Homeland Security
Requiem for Korematsu?
Stephen Dycus reviews Professor Eric K. Yamamoto’s timely book In the Shadow of Korematsu: Democratic Liberties and National Security, published just weeks before the Supreme Court decided Trump v. Hawaii. Dycus draws out the book’s core themes, highlighting Yamamoto’s analysis of the Korematsu decision and its continued relevance in American jurisprudence. The review concludes with… Continue reading Requiem for Korematsu?
Before Privacy, Power: The Structural Constitution & the Challenge of Mass Surveillance
The rich legal literature that has grown up to assess the constitutionality of bulk communications collection by the government has focused overwhelmingly—and understandably—on the challenge such programs pose to particular claims of individual right against the state, yet attempting to describe what seems troubling about bulk collection in terms of individual rights alone has significant… Continue reading Before Privacy, Power: The Structural Constitution & the Challenge of Mass Surveillance