Maj. Jeremy Watford examines the historic divide between military operations and intelligence collection—particularly when it comes to statutory authority and oversight responsibilities—and discusses how modern cyber operations complicates this separation. Watford proposes a new framework to resolve the current tensions in military and intelligence operations largely caused by “bureaucratic territoriality” and to account for the… Continue reading A New Framework for Cyber Operations: Reevaluating Traditional Military Activities and Intelligence Collection in the Digital Age
Category: Issue Archive
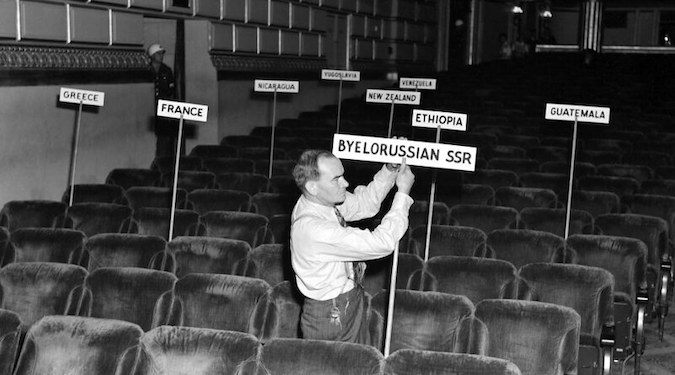
The San Francisco Conference and the Evitable UN Vetoes
Robert A. James reviews the surprising history of the United Nations Security Council veto, the five permanent members solution, and the various alternatives proposed during the discussion. Although the current Security Council format appears historically inevitable, there is ample evidence of alternative formats suggested at the time of the construction of the United Nations. Beginning… Continue reading The San Francisco Conference and the Evitable UN Vetoes
Influence, War, and Ethics
Beba Cibralic contends existing international law frameworks are inadequate for explaining why certain foreign information-based influence campaigns are impermissible or troublesome. Moreover, Cibralic posits the warfare paradigm is both limiting and potentially dangerous. Cibralic proposes reframing the conversation about foreign information and influence campaigns to focus not on the nationality of the speaker or the… Continue reading Influence, War, and Ethics